Zero Trust IT Security

Zero Trust is not a product, it is a combination of tools and a philosophy of how to manage your environment covering multiple areas – Identity, Perimeter, Threat Hunting, Application Control, Secure Access, Storage Control
The core concept of zero trust is simple: assume everything is hostile by default. It’s a major departure from the network security model built on a centralized data server and secure network perimeter
Only approved applications are allowed to run inside your network, and what these applications are allowed to do is controlled so they can only do what they are required to do. As an example, your email account should not be able to access your Backup files or launch a new application. It should only be allowed to do what it is intended for.
Zero Trust approach treats all traffic, even if it’s already inside your network, as hostile. Workloads are blocked from communicating until they are validated by a set of attributes, such as a fingerprint or identity and all applications are restricted from accessing resources that are not approved.
Once approved, applications can only function as permitted and access to resources otherwise available to users on your network such as Backup Software, USB Drives, Shared Folders, and Operating System files are blocked.
Using this method we block ransomware from running even if it does get inside your network.
A Zero Trust architecture follows the maxim “never trust,” always verify.”
How Do Breaches Happen?

Hacks today are different than they were 5 years ago. Many organizations were just using Antivirus software and a firewall as their main points of Threat Hunting and protection.
Today’s hacks are dominated by compromising legitimate applications, phishing emails, visiting compromised websites or uploading malicious files through an external device like a USB drive.
Threat Hunting products cannot stop many of the attacks because often is no attachment or file to scan. It is also common that a compromised user or the users computer is attack vector. If you can modify a file, run a program, connect to the internet, visit a malicious website, so can the hacker.
With Administrative rights, a hacker can do anything that the computer is allowed to do.
The main goal of any compromise is to capture your Important company data. Once a hacker gains access to your systems they will move laterally throughout the network and start to learn your operations, who signs off on cheques, bank access, patient records, vendors you deal with etc. After learning everything needed, they:
- Upload your data to their cloud account.
- Modify or delete your backup data so that it is useless.
- Encrypt your data and lock your machines.
- Demand a ransom to unlock your files.
If you pay the ransom, (less than 50% success rate) you may regain access to your files. Then the second demand comes in the form of a request for more payment in order to prevent them from publishing your patient data to the internet
This exposes you to further costs and potential government penalties (PHIPA Legislation) in addition to the cost of downtime and remediation of the breach.
How Do We Prevent This?
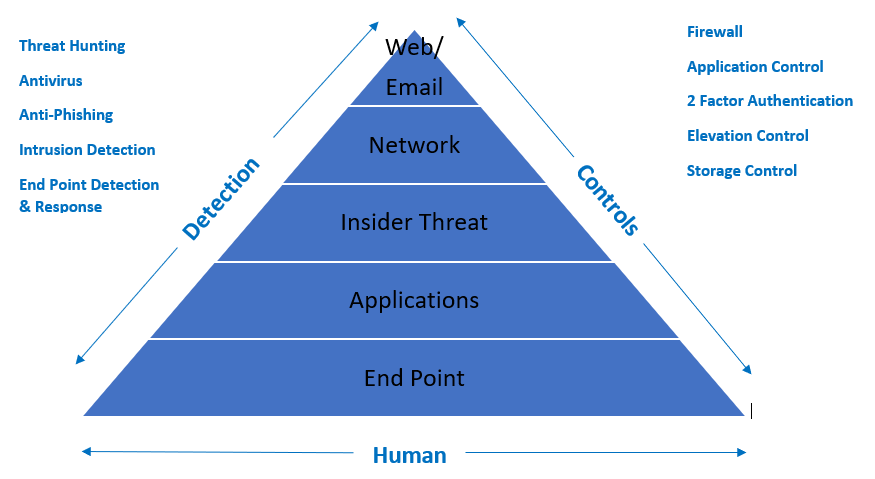
To implement a Zero Trust environment for you, we use a comprehensive data checklist to identify your existing posture and we present you with summary of recommendations that can be implemented quickly.
This includes:
- Incorporate all of your existing infrastructure adding to it only where necessary and approved
- Complete suite of application control tools along with secure storage and secure network access
- Next Generation Firewall for Perimeter and network protection
- Employ 2 Factor Authentication for all users
- Lock down access to important files like backups, Operating System components (PowerShell, registry files), USB storage devices, internal file shares
- Provide secure remote access with no VPN’s
- Teach users how to identify potential threats – and alternatives for when they have a question
This is part of our Managed Security Services offering that includes all standard support for all your IT systems as well as 24×7 monitoring, system and application patches, strategic guidance and more.
You Can Act Now or React Later
Less than 60 % of malware is caught by Antivirus – Any Threat Hunting product is always behind in identifying new threats as more than 100,000 are identified daily
Legitimate tools like email, Zoom, Remote Access programs, Microsoft Office programs and social media are being used to compromise systems now – This is the current biggest threat.
The best way to protect you is to control what applications can run and how they run, and disallow any executable from running which includes ransomware
Don’t wait until you become part of the growing number of practices affected by this menace
Security is only as strong as the weakest link. In many cases that weak link is uneducated users that do not know how to identify potential threats.
We take the threat of breaches out of the users hands and mitigate it through our Zero Trust offering.
